User Tools
Sidebar
This is an old revision of the document!
Firewall
The Firewall page allows you to configure options to protect or facilitate various types of network communications.
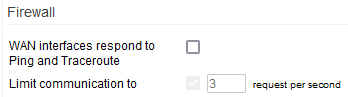
Firewall
WAN interfaces respond to ping and traceroute: If enabled, this allows your device to reply to ICMP ping and traceroute request packets from Internet hosts. This is necessary for ping and traceroute to work from the Internet.
Limit communication to: This specifies the maximum number of requests per second to which the Firewall will reply. Setting a limit number is recommended to prevent DDoS attacks.
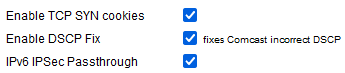
Enable TCP SYN cookies: Enabling this uses the “SYN cookies” technique to protect the router from SYN Flood attacks. This function encodes information from the SYN packet into the (SYN/ACK) response. This is a standard method for preventing SYN floods. However, it has certain limitations which may cause issues with some old TCP/IP stacks.
Enable DCSP Fix: Checking this enables a workaround for packet marking, a well-known issue related to DSCP when connected to Comcast.
Allow DHCP Spoofing:
Smart MTU black hole detection:
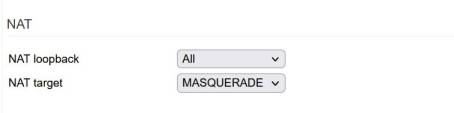
NAT
NAT loopback: This technique allows LAN devices to access each other via the router's WAN interface. Also known as “Hairpinning”, this is commonly used when connecting to the DDNS domain of your router from the LAN. These days, this legacy setting is almost never needed. It also can create speed bottlenecks.
- All
- Forwarded Only
- Disabled
NAT target - This defines the way NAT is implemented for use during loopback. Masquerade is the default, but involves an additional lookup. ad the mapping of done towards an interface. SNAT is minutely faster, as the NAT mapping points directly to the destination IP and so it bypasses the lookup stage. However, SNAT is less reliable than Masquerade.
Multicast
Enable IGMP proxy - Checking this enables the IGMP (Internet Group Management Protocol) service.
LAN0 - LAN3 Specifies which bridges will participate in IGMP, with the router acting as a proxy between selected LANs. This allows IGMP to work between VLANs.
- LAN0 - Checking this means the LAN0 bridge will participate in IGMP proxy.
- LAN1 - Checking this means the LAN1 bridge will participate in IGMP proxy.
- LAN2 - Checking this means the LAN2 bridge will participate in IGMP proxy/
- LAN3 - Checking this means the LAN3 bridge will participate in IGMP proxy.
Enable quick leave - This is a feature of IGMP v2 and later. Enabling this allows the router to stop streaming multicast to an IP address as soon as that device sends a “quick leave” IGMP packet.
Custom Configuration - This option allows you to set advanced parameters for the IGMP proxy daemon. Consult official IGMP documentation before using this.
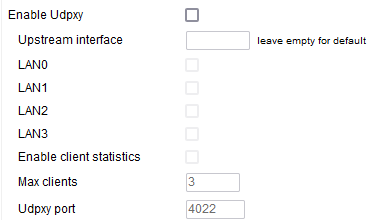
Enable Udpxy - Like IGMP proxy, Udpxy allows multicast communications between devices on different VLANs. Since their behavior is very similar, you are advised to use either Udpxy or IGMP proxy, but not both at once.
Upstream interface - Here, enter the stream source is expected to live. (Default: blank).
LAN0/LAN1/LAN2/LAN3 - This specifies the location the streaming clients are expected to be found.
Enable client statistics - Enabling this causes FreshTomato to collect statistics about Udpxy clients.
Max clients - This represents the maximum number of simultaneous Udpxy clients. Udpxy is is a lightweight protocol, and only works well for a limited number of clients. For this reason, you might want to impose a maximum limit.
Udpxy port- This specifies the port on which you can recive Udpxy information from your router.
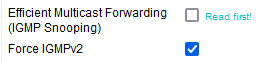
Efficient Multicast Forwarding (IGMP Snooping) - IGMP snooping allows the router's switch to facilitate discovery of Multicast IGMP clients. The goal is to send multicast traffic only towards ports with at least one multicast subscriber?
Caution is advised, as often, UPnP is the only significant multicast application in use on a home network. Thus, multicast configuration issues or other deficiencies can appear as UPnP issues, when they're actually underlying network issues.
If IGMP snooping is enabled on a (wireless router)/switch, it will interfere with UPnP/DLNA device discovery (SSDP) if incorrectly or incompletely configured (e.g. without an active querier or IGMP proxy), making UPnP appear unreliable. Typical scenarios observed include a server or client (e.g. smart TV) appearing after power on, and then disappearing after a few minutes (often 30 by default configuration) due to IGMP group membership expiring. On this very topic please beware of the wireless multicast forwarding under Advanced Wireless
Force IGMPv2 - IGMPv2 enhances the IGMP communication supporting additional messages/behavior to optimise the end-to-end communication between client and server. Possibly the most important being the “Group Leave” message which is lacking instead in IGMP v1.